Phishing Campaign in Google Ads Exploits GoDaddy's ManageWP Credentials
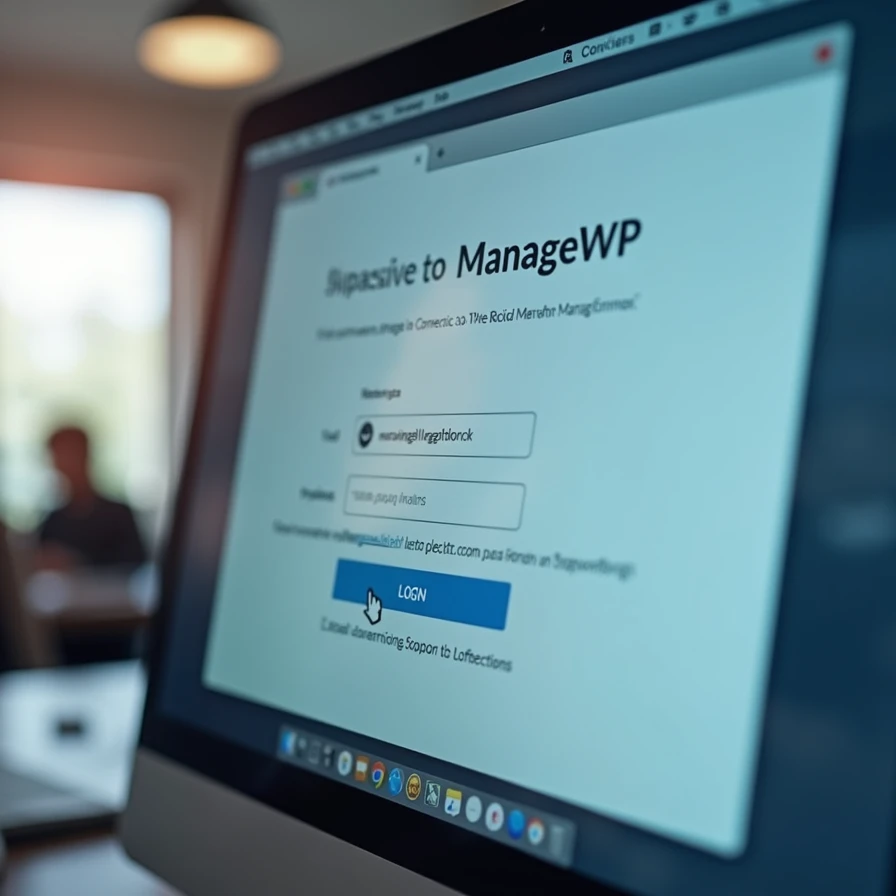
A phishing campaign is leveraging sponsored Google Ads to impersonate ManageWP login pages, aiming to steal credentials and potentially compromise numerous WordPress websites managed through the platform.
By Carlos "Emérito" López Lovera•6 may 2026•4 min read
Key Takeaways
- Threat actors are abusing the Google Ads platform to distribute phishing links targeting ManageWP users.
- The primary objective is the theft of ManageWP login credentials, enabling unauthorized control over multiple WordPress sites.
- The incident highlights a critical vulnerability in the digital chain of trust, where legitimate advertising platforms are exploited for malicious activities.
Incident Analysis
The recent phishing campaign, documented by Bleeping Computer, leverages the Google Ads platform to compromise credentials for ManageWP, GoDaddy's comprehensive WordPress management service. Threat actors are purchasing advertising space on Google Search using strategic keywords related to ManageWP. These ads, visually indistinguishable from legitimate results to the average user, redirect to fraudulent domains that replicate the ManageWP login interface. The attack methodology focuses on URL spoofing and the visual mimicry of the authentication page, aiming to induce users to enter their credentials into a form controlled by the attackers.
This attack vector is not unprecedented; the abuse of legitimate advertising platforms like Google Ads to distribute malware or facilitate phishing campaigns has been documented previously. The distinction here lies in the target: ManageWP. This platform centralologizes the administration of multiple WordPress installations, meaning a single credential compromise can grant attackers access to an entire portfolio of websites, significantly amplifying the potential impact of the intrusion.
Technical and Operational Context
From a technical perspective, the success of this campaign relies on several factors. First, the effectiveness of sponsored SEO in Google. Phishing ads appear prominently in search results, often above legitimate organic results, increasing visibility and the likelihood of user interaction. Second, the sophistication of the phishing page design. These replicas are often nearly perfect, making it difficult to identify the forgery without a meticulous inspection of the URL and security certificates.
As a remote management tool, ManageWP operates with elevated privileges over the connected websites. Unauthorized access to a ManageWP account could allow attackers to perform various malicious actions: code injection, malware distribution, content modification, sensitive data extraction from WordPress databases, or even taking control of underlying servers in certain configurations. This represents a critical vulnerability in the digital supply chain for a significant segment of the web, given that WordPress powers approximately 43% of all websites.
Economic and Market Implications
The economic consequences of a successful compromise are multifaceted. For businesses and professionals using ManageWP, an attack would result in operational disruptions, data loss, reputational damage, and potential legal liabilities. Restoring compromised websites involves direct costs in time and security resources. Furthermore, the loss of customer trust can lead to decreased revenue and market share.
For GoDaddy, as the provider of ManageWP, the incident poses reputational and security challenges. Although the vulnerability lies in the exploitation of an external platform (Google Ads) and social engineering, public perception may associate the risk with the security of their services. This could drive pressure to implement more robust multi-factor authentication (MFA) measures and actively educate their user base about phishing threats. The WordPress management services market is competitive; security incidents can influence client decisions regarding provider selection.
For Google Ads, this event underscores the need to improve detection and mitigation mechanisms for malicious ads. The permissiveness of its platform toward the proliferation of phishing campaigns negatively impacts the trust of both users and legitimate advertisers and could attract stricter regulatory scrutiny regarding the responsibilities of platforms in advertising content moderation.
Mitigation and Future Outlook
Mitigating this type of attack requires a multifaceted approach. ManageWP users should implement multi-factor authentication (MFA) on their accounts, rigorously verify URLs before entering credentials, and access the platform directly via bookmarks or the official URL rather than through search links. Service providers like GoDaddy must intensify cybersecurity awareness campaigns for their users.
From a platform perspective, Google Ads must refine its fraud detection algorithms and ad review processes to proactively identify and block ads directing to phishing domains. Implementing more robust identity verification technologies for advertisers could reduce the ability of malicious actors to operate. The evolution of these phishing campaigns demonstrates the constant adaptation of attackers to existing defenses. Continuous vigilance and the implementation of advanced security protocols will be essential to counter future iterations of these threats.
📖 Key Terms Glossary
❓ Frequently Asked Questions
What is the phishing campaign targeting ManageWP?
It is a cybercrime operation using fraudulent Google Search ads to redirect users to fake ManageWP login pages to steal their credentials.
How is this phishing campaign distributed?
It is distributed through Google Ads. Attackers purchase keywords related to ManageWP, ensuring their malicious ads appear at the top of search results.
What is the risk of this campaign for users?
The primary risk is the loss of control over multiple WordPress websites. By obtaining ManageWP credentials, attackers can access, modify, or compromise all sites managed under that account.
Support independent journalism 💸
The crypto ecosystem is volatile. If you decide to invest, do it safely using our affiliate links in the most trusted exchanges. You get a welcome bonus and we get a small commission.
Disclaimer: This content is not financial advice. Do your own research before investing.